
Tragedy Strikes: 2 Malaysian Military Helicopters Collide in Fatal Accident
Brief: 2 Malaysian Military Helicopters Collide During a parade rehearsal in Malaysia on Tuesday, … Read more

On Monday Morning 5 People Found Dead In Oklahoma City Including Two Children
Brief: On Monday morning 5 People Found Dead in Oklahoma City Home. Sgt. Gary … Read more

Google Fired over 20 employees following sit-in demonstrations at its New York and California.
Brief: Google has terminated over 20 employees at its New York and California offices. … Read more

Terry Anderson Dies: Longest-Held Western Hostage in Lebanon Passes Away at 76
Brief: Terry Anderson dies at 76 on Saturday at his residence in Greenwood Lake, … Read more

“Deadpool and Wolverine” Movie has Dropped its Second Trailer
Marvel’s Deadpool and Wolverine Clash in Explosive Third Film Trailer Marvel’s highly anticipated “Deadpool … Read more

Denver Broncos Strategy for Future with Zach Wilson Acquisition
Denver Broncos Strategy For Quarterback with Zach Wilson Trade The Denver Broncos’ decision-makers have … Read more

Grindr Data Privacy Breach Sparks Legal Action and Privacy Concerns
Grindr Data Privacy Breach: Faces Legal Action Grindr, the leading dating app serving the … Read more
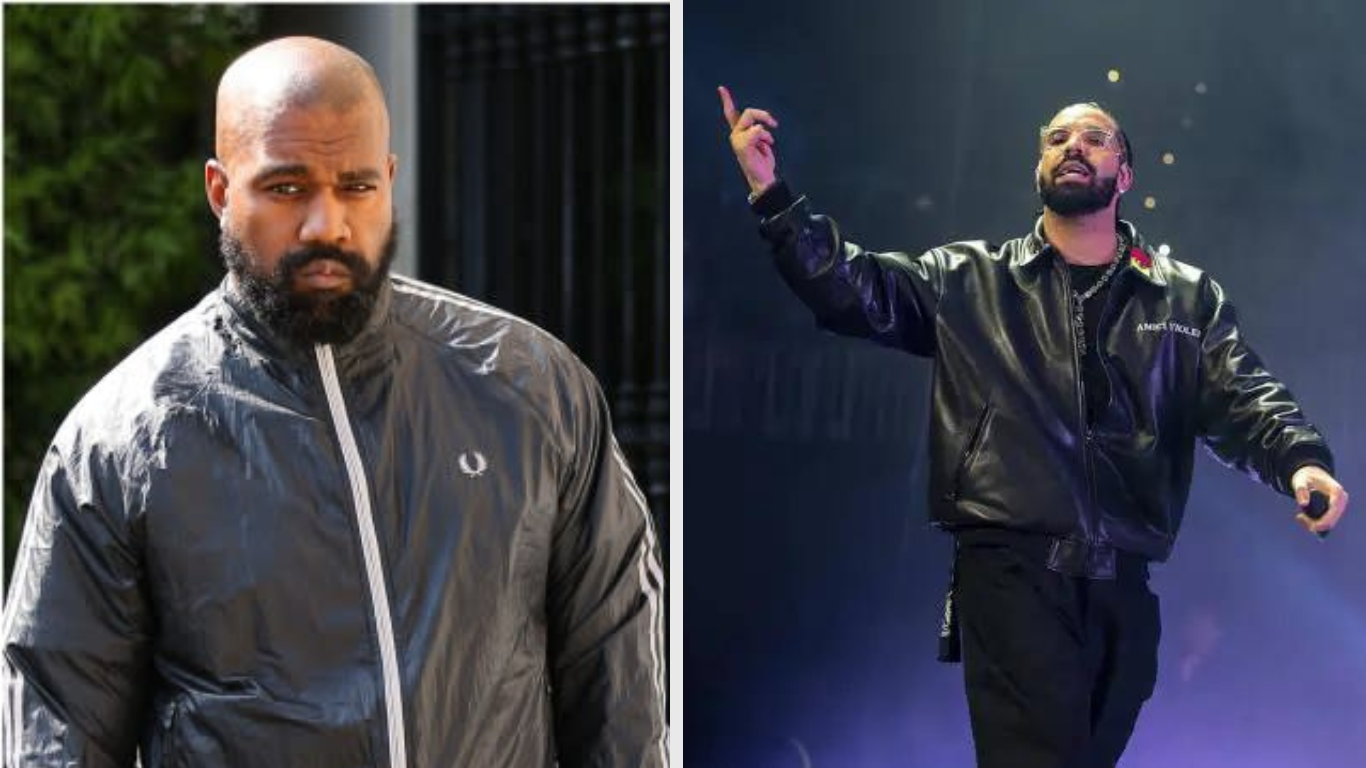
Hip-Hop Feud Escalates as Kanye West Enters Fray with Drake Diss
Kanye West Joins Feud, Takes Aim at Drake In the ongoing saga involving Drake, … Read more
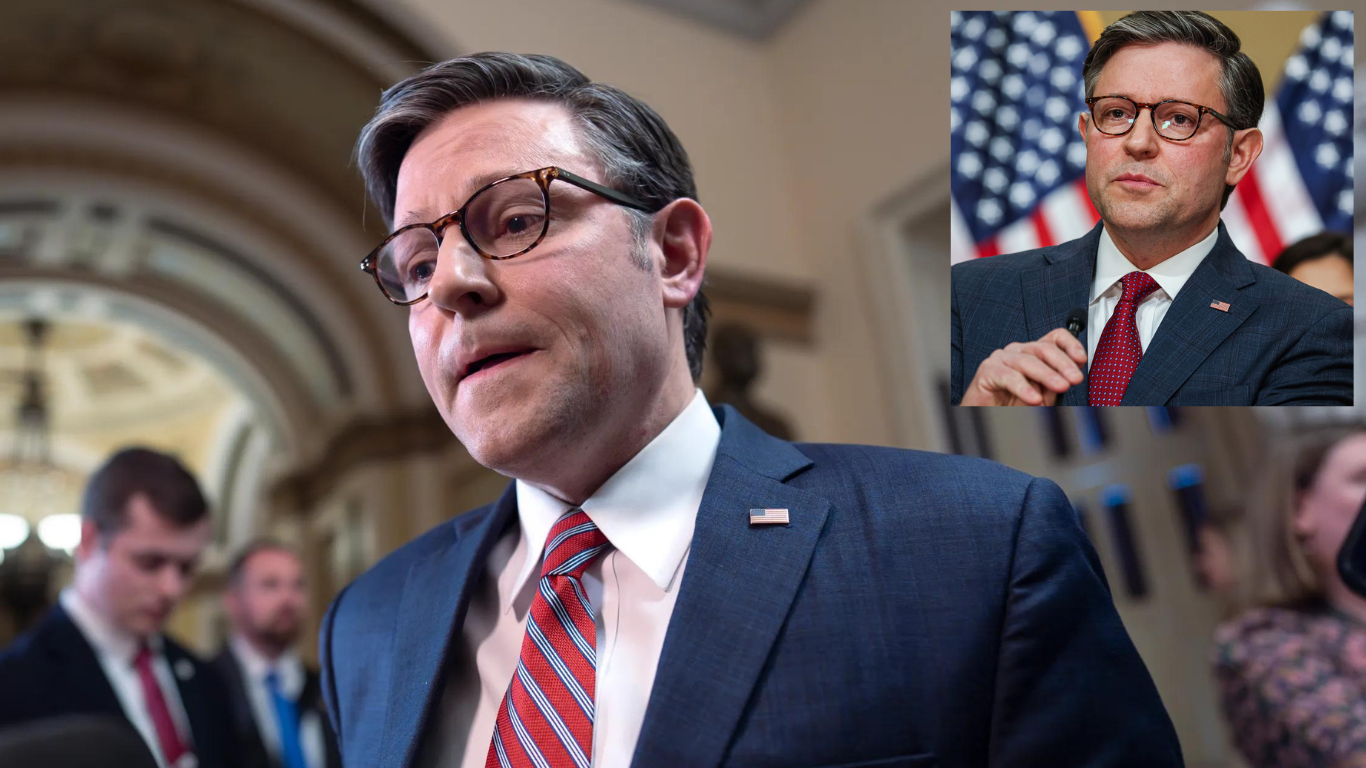
U.S. Speaker Mike Johnson’s Ukraine Deal Could Have Political Consequences
US Speaker Mike Johnson may pay political price for Ukraine deal Bipartisan Support for … Read more
