Simple mail transfer protocol (SMTP), is used to send emails through the internet all over the world.
- Simple mail transfer protocol (SMTP), is an email protocol that allows users to send emails over an internet connection.
- Simply stated, SMTP allows clients and email accounts to share information more efficiently by using a set of rules.
- The full form of SMTP stands for Simple Mail Transfer Protocol.
This article will discuss the uses and best practices of SMTP (Simple Mail Transfer Protocol).
What Is SMTP (Simple Mail Transfer Protocol)?
Simple mail transfer protocol (SMTP), is an email protocol that allows users to send emails over an internet connection.
Simply stated! SMTP (Simple Mail Transfer Protocol) allows clients and email accounts to share information more efficiently by using a set of rules.
This protocol is used in conjunction with IMAP (internet message access protocol) and POP (post office protocol).
SMTP (Simple Mail Transfer Protocol) is a protocol that empowers you to send emails.
Many popular email clients, such as Microsoft Outlook, Google Gmail, and Yahoo Mail, use SMTP to send (or push') emails to the receiver.
SMTP (Simple Mail Transfer Protocol) servers are responsible for the transmission, receipt, and relaying of emails to other applications (known as clients) within a network.
- Imagine an SMTP server as a real-world postal office. A letter would need to be sent from City 1 to City 2. First, the letter would reach City 1's local post office.
- The letter would then be processed at that local post office and shipped to City 2. The letter would then be processed and sent to the City 2 post office.
- SMTP servers perform the same process, but message transmission takes only a few moments rather than a few weeks.
- SMTP ports, on the other hand, serve as communication endpoints to handle email data transfer over SMTP between servers across a network.
Outgoing emails are transmitted via ports 465 and 587. However, messages between email servers can be sent using port 25.
How does SMTP Work?
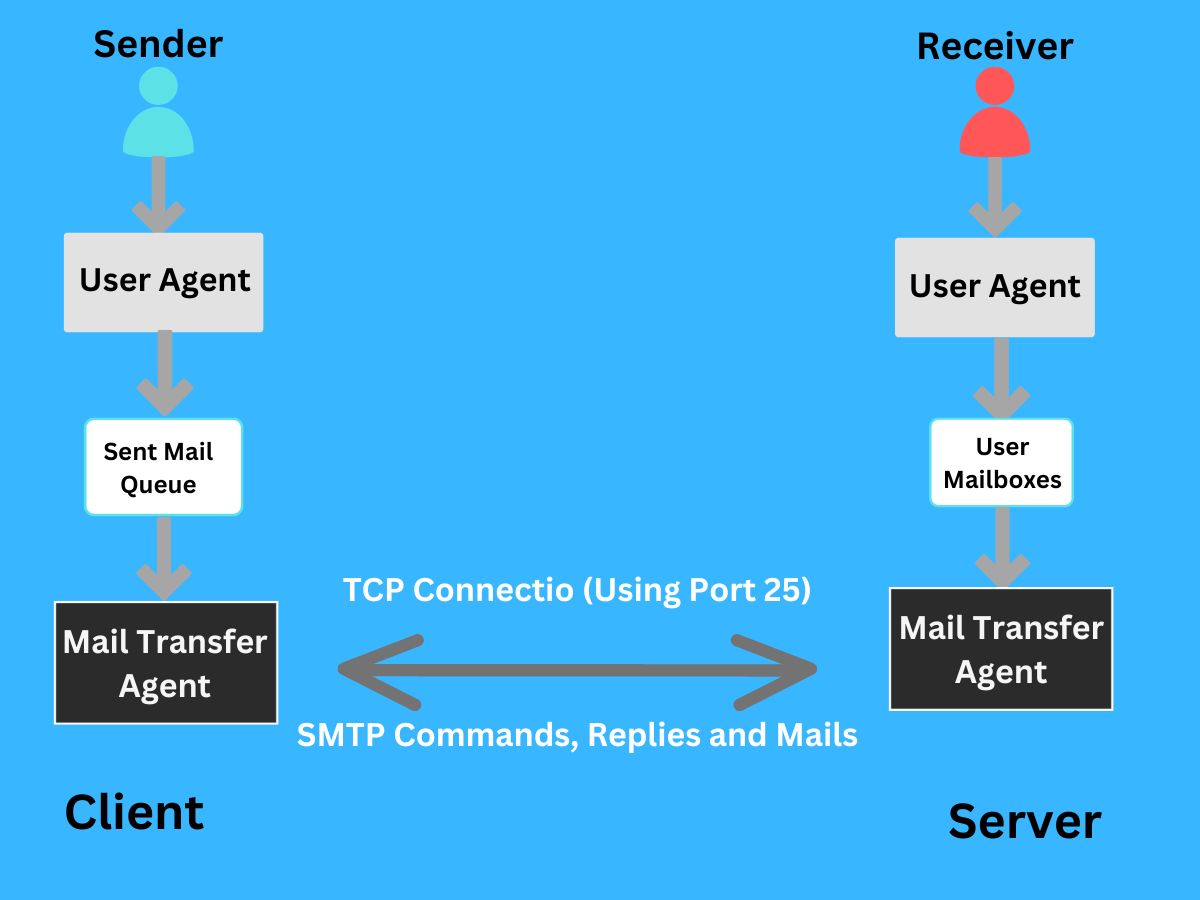
First, a user must set up an SMTP Server. After that, email clients can connect to it.
Once that is done, the user can press the send button on an email. An SMTP connection between the client's computer and the server is established to allow the email to be sent.
The SMTP connection is built on a transmission protocol (TCP) connection.
Once the SMTP (Simple Mail Transfer Protocol) connection has been established, the client transmits commands to the server. These instructions allow the transfer of information such as the sender's and recipient's email addresses and the content of the email.
MTA can be spelled message transfer agent (or mail transfer agent) and is responsible for verifying that both email addresses come from the same email domain such as Gmail. The email will be sent instantly if both addresses come from the same domain.
If the domain name system is not used, the server will use it to identify the domain receiving the email, and then the email will be transmitted to the correct server.
What are SMTP, POP, and IMAP?
SMTP is not the only common email protocol. IMAP and POP are also popular. SMTP (Simple Mail Transfer Protocol), however, is a unique email protocol. It is used to 'push' emails (sending them) between unknown email servers.
POP and IMAP, on the other hand, are used to 'pull (receive), an email from the recipient party from their server.
POP and IMAP can only be used to transfer emails to verified servers. They cannot be used to transmit messages outside the network of the user.
To receive emails, the post office protocol (POP) is used. POP3 is the latest version. The protocol's operation mimics that of a real-world postal office. POP3 will pull and hold emails until clients are picked up.
Emails can be downloaded and saved to the local system. This makes it ideal for users who only use one endpoint to access their email. Enterprises can also use POP to allow employees to access their email offline. Unlike SMTP (email sender), POP is a message access protocol (email recipient).
This means that SMTP (Simple Mail Transfer Protocol) can be used twice: once when data is being transmitted between the sender's email server and the sender, and again when data is being transferred and a connection with the recipient.
POP, on the other hand, is only used once -- to transfer data between the recipient and their email server.
The internet messaging access protocol (IMAP), stores email on a server that users can access and configure.
IMAP is different from POP. It uses a Cloud Server to allow email authentication and categorization depending on the device type.
IMAP is preferred to POP due to its efficiency and ease of use. Like POP, IMAP is a message access protocol (email recipient). These are some SMTP protocols now let's look further on its uses.
What are Uses of SMTP (Simple Mail Transfer Protocol)?
SMTP is a widely used protocol that plays a vital role in email communications. Let's take a look at five of the most important uses for SMTP.
1. Email Delivery and Transmission
SMTP (Simple Mail Transfer Protocol) is used primarily to send emails between clients and servers.
It is used for personal and professional email accounts.
Once an email has been sent, it reaches an SMTP Server, which uses a set of rules to determine where the email should be sent next.
The email is sent to the recipient's local email client or their email account.
2. Email Routing
SMTP (Simple Mail Transfer Protocol) can route emails through multiple networks before they reach their destination inbox.
This allows SMTP to be used to send emails to clients and servers located in different geographic locations.
SMTP (Simple Mail Transfer Protocol) can be used in combination with IMAP, POP, and other protocols to route emails. This allows for efficient retrieval and management of emails.
3. Email Authentication
SMTP allows servers to authenticate the sender and encrypt/decrypt emails to protect data privacy.
SMTP (Simple Mail Transfer Protocol) makes it harder for spammers to read and intercept emails. It also helps prevent phishing attacks.
SMTP wasn't always the torchbearer of email authentication. When SMTP was first introduced in 1981 it used open relays.
This meant that users were not authenticated and all email messages were sent regardless of their address. This allowed mass spam mail to flood the system.
With time, new versions were introduced to SMTP, including SMTP after-POP (ESMTP), extended SMTP(ESMTP), as well as SMTP–AUTH (also known under ASMTP).
These newer protocols required users to have a password or another authentication mechanism to log in to the SMTP server at an email service provider.
There was no need for zero SMTP (Simple Mail Transfer Protocol) authentication. Any unauthorized party could send an email to an open server using a fake email address.
Only verified users were allowed to send emails via SMTP servers after new authentication procedures were implemented.
This created a barrier of entry and stopped low-level bad actors from sending malicious or unsolicited messages. Emails sent from servers not using SMTP-AUTH are often returned to senders with an 'authentication failure' error.
Most email programs automatically set up SMTP (Simple Mail Transfer Protocol) authentication for users when they create new accounts.
Users who set up email accounts using a third-party client like Mozilla Thunderbird or Microsoft Outlook must ensure that SMTP-AUTH has been activated. This information can be found on the support pages for the particular email application.
4. Email Security
Email security is essential, as email is one of the most used communication methods in the world. This is especially true for enterprise communications. SMTPS is a way to secure SMTP (Simple Mail Transfer Protocol) via transport layer security (TLS).
SMTPS protects email from being altered or rerouted to an unauthorized intermediary. SMTPS prevents attackers from attempting to exploit unencrypted email messages by infusing malicious SMTP commands while the email is being transmitted between servers.
Emails that contain forms are a common target of such attacks since these emails often have built-in vulnerabilities.
Emails without SMTPS are more vulnerable to spamming from a vulnerable domain, silent theft of sensitive information, and phishing attacks. TLS must be enabled on the user's email server to enable SMTPS. TLS activates the SMTP protocol on the transport layer and SMTP is 'wrapped within' a TLS link.
5. Email Marketing
Enterprises, whether online or offline, use email to communicate with customers. It is crucial for business owners that they ensure their emails are sent securely and delivered to their customers' inboxes reliably.
SMTP (Simple Mail Transfer Protocol) is a key component of email marketing campaigns in all industry verticals. It ensures that emails are delivered to customers securely and without error. High deliverability is a major reason to use SMTP for email marketing. SMTP-powered email solutions that are highly effective allow marketers to enjoy high deliverability.
Advanced SMTP relay servers provide the tools needed to maintain a sending address. This can help reduce spam folders. SMTP (Simple Mail Transfer Protocol) servers increase deliverability by supporting account validation, domain authentication, and email authentication protocols like DKIM, DMARC, and SPF.
Email marketers love log retention, which is another important feature of SMTP servers. These logs include metrics like open rate, CTR, and unsubscribe rates. Marketers prefer SMTP email servers to retain logs for longer periods, so users can go back and review them in the event of an issue.
Many SMTP servers provide a 30-day retention period. However, others allow unlimited log retention and offer the ability to set retention policies.
Finally, SMTP (Simple Mail Transfer Protocol) solutions for email marketing can be used by both non-tech-savvy marketers and business owners. The SMTP solutions simplify email sending with an easy-to-use interface, simplified onboarding, and responsive support staff.
What are SMTP Best Practices?
The following simple mail transfer protocol (SMTP), best practices can be used to manage an email server and improve the sender's reputation. This will ensure smooth email delivery. Let's get started.
1. Misuse Prevention for Open SMTP Relays
Residential ISPs and Cloud providers block SMTP port 25, to prevent spamming and open SMTP relays being misused.
Although some providers permit users to open port 25, this is usually a multi-layered process to reduce the chance of misuse.
Service providers might request proof of identity or payment method verification as well as the reason for an outbound port 25.
If there is evidence of spamming or a compromised server, the outbound SMTP (Simple Mail Transfer Protocol) port 25, can still be closed.
Users must also exercise caution when configuring servers and try to avoid their servers becoming open relays. Server setup errors can result in the misuse of open relays, making security settings useless.
SMTP (Simple Mail Transfer Protocol) diagnostic tools are generally useful for testing SMTP configurations for flaws.
2. Professional Mailing Solutions
Users should not be concerned about outbound SMTP port 25 being blocked. Ports 465 and 587, as well as non-standard ports that can be used to send emails through a relay, are still available.
The mail transfer agent (MTA), for example, can be set up to use port 587 as a mail service for securely relaying emails.
Users can also choose not to have their SMTP (Simple Mail Transfer Protocol) server. Users can instead, depending on their use case, consider using a professional mailing service.
A specialized service provider can help both transactional emails and marketing campaigns perform better and deliver more results.
3. Matching Forward DNS and Reverse DNS
Also known as forward-confirmed reverse DNS, RFC 1912 makes it a priority to ensure that it is valid and matches forward DNS.
An understanding of the key request to comments (RFC), documents that system administrators must understand can help avoid spammers from spoofing SMTP.
4. Reverse DNS and HELO String Match
An SMTP (Simple Mail Transfer Protocol) server must 'announce' the name of an email sent to it using either the HELO/EHLO command.
When DNS is correctly configured with a fully qualified domain name (reverse DNS), the sender can comply with RFC 2821, and use it as their HELO/EHLO string.
This adds another layer of verification, as it confirms the identity of the server.
5. Sender Address Verification (SAV).
Some SMTP (Simple Mail Transfer Protocol) configurations do not include a default way to authenticate using the MAIL FROM address. This is where Sender Address Verification (SAV), which allows users to connect to the correct return host and confirm that the site accepts email from the address, can be very useful.
SAV has some loopholes. SAV can be bypassed by attackers who simply send emails to valid MAIL FROM addresses. Spammers can target any address that is already in use.
It is recommended that you take extra care when using SAV. Other authentication methods are also available.
6. Secure SMTP Using SSL/TLS
Email providers have taken steps to improve the security levels of SMTP. One such measure is the secure sockets layers (SSL). SSL v2.0 was originally developed by Netscape in 1995. It quickly became a popular feature for email clients.
SSL lost popularity over time and was eventually deprecated in 2015. In 2015, TLS was replaced by transport layer security (TLS). TLS was continuously improved upon after its release. Today, TLS version 3.0 is an industry-standard.
Although SSL is still available, many vulnerabilities make it less popular than TLS. It is important to note that not all providers use SSL or TLS interchangeably when choosing an SMTP solution. A service provider might market their security protocol as SSL but may also offer TLS.
TLS is required to ensure that email security is maintained. This enables encryption between the client and server. If malicious actors can breach other layers of SMTP (Simple Mail Transfer Protocol) security, they will only be able to access the content of the email in a seemingly random location.
They would still be able to create havoc to a certain degree, but TLS-powered email encryption reduces SMTP's attack surface and improves data protection.
TLS also supports digital certificates, which provide an additional layer of security. These digital certificates provide a tangible identity for each step and allow what is called a handshake.
What is a Handshake? How does it Work?
In computer science, a handshake is a process that establishes a communication session between two devices. A handshake typically involves a series of steps where each device confirms its identity and the parameters of the communication to the other.
Handshakes are used to establish secure connections, such as SSL/TLS connections between web browsers and servers, or to negotiate parameters in a network protocol. The exact steps in a handshake can vary depending on the specific technology or protocol being used.
As we have already explained, email is transmitted via SMTP (Simple Mail Transfer Protocol). It starts from the sender’s email client and moves to the sender’s email server. Then it goes to the receiver’s email server. Finally, it goes to the receiver’s email client. Each stage is marked with a new connection.
TLS-powered SMTP (Simple Mail Transfer Protocol) requires that both parties establish trust. The sender's email client must confirm that it is communicating with the SMTP server and not another network entity that is emulating. Servers would also need to verify each other's authenticity before sending an email. This is done by a handshake.
👉 These are the steps to follow when you establish a handshake:
- An email client sends details about the SSL/TLS versions that it is compatible with and the encryption types it supports.
- The server replies with a message that contains a public encryption key as well as a TLS digital cert.
The certificate's legitimacy is verified by the client. If the certificate is valid, the client creates a "shared secret key" using the public encryption keys of the server. - The server decrypts and receives the shared secret key. Both parties can now use the shared secret key to encrypt and decrypt emails they exchange.
- Both parties use different keys to begin the process. Once each step is completed successfully, the shared key is used to enable encryption to be synchronous, faster, and more efficient.
Takeaway
SMTP (Simple Mail Transfer Protocol) is a protocol that allows email delivery and transmission. It is used by the majority of popular email clients, such as Microsoft Outlook and Google Gmail.
To use SMTP (Simple Mail Transfer Protocol), a user needs to set up an SMTP Server and configure their email client so that it can connect to it. The client sends commands to the server which allow the transfer of information such as email addresses and email content.
The email is sent immediately if the email addresses come from the same domain. If they are not, the server uses the domain name system (DNS), to identify the recipient domain and send the email to the correct server.
Unlike SMTP (Simple Mail Transfer Protocol) which is used to send emails, IMAP and POP are used to retrieve emails from a server. POP stores and downloads email locally, while IMAP can manage emails on a server.
SMTP (Simple Mail Transfer Protocol) was initially an open protocol that required no authentication. However, later versions of SMTP, ESMTP, and SMTP–AUTH introduced authentication mechanisms to protect against spamming and phishing attacks.
SMTPS (Secure Mail Transfer Protocol) is a way to secure SMTP with transport layer security (TLS). This protects against attackers who modify or redirect email content to unauthorized intermediaries. SMTP is used extensively in enterprise communications and email marketing to send promotional emails and newsletters.
SMTP (Simple Mail Transfer Protocol) can be used to manage an email server. There are several best practices. These best practices include using professional mailing solutions, matching forward DNS and reverse DNS, matching HELO strings and reverse DNS, taking care of sender addresses verification (SAV), and securing SMTP via secure sockets layer or transport layer security.

